Tor vs VPN: which is better?
Is it better to use Tor or a VPN to protect your privacy when you are online? This guide will show you how they work and which is better for your situation. If you want to skip the guide and get the solution that is best for most people, download Hotspot Shield now.

How Tor works
The name “Tor” comes from the acronym of the original project name, “The Onion Router.” It is called an “onion” router because your data is routed through multiple layers of security before reaching its final destination.
Tor primarily protects you against “traffic analysis,” which can reveal your personal identity and location by monitoring your data at different points between your computer and the websites you visit. This diagram shows you how Tor works.
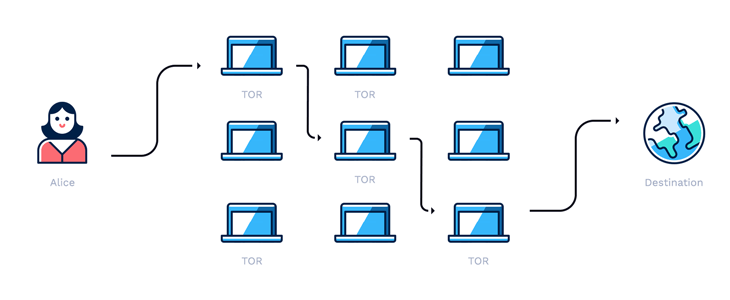
The Tor network is accessed by downloading their free browser. Once you place a request for information in the browser, the browser contacts a random Tor server, or node. That node then passes your request to the next randomly selected node and so on.
Your request will be passed between several nodes before reaching its final destination. The same thing happens when data is passed back to you.
These multiple “hops” are what help keep your identity safe. Each node only knows the IP address of the previous node and the IP of the next node. So it is impossible for any one server to know where the data originally came from and the ultimate destination.
This way, your traffic cannot be analyzed while it is being transmitted. Your data is also encrypted while it is passed between these intermediate nodes.
However, there is one potential vulnerability in the Tor network and that is the exit node. This is the last node to handle your data, before it reaches the final destination.
The data on this node is completely decrypted, so if you are not using a HTTPS connection, your information will be totally exposed to the person running the exit node.
Tor advantages
- Since it is a distributed network run by volunteers, it is extremely difficult for any government or organization to shut it down.
- The routing method does not reveal your IP address to the websites you visit.
- It’s free to use the software and network.
- Allows you to access geographically restricted websites and content.
Tor disadvantages
- Tor is very slow compared to a VPN. Since your data is routed through multiple relays, each with varying bandwidth, you are at the mercy of the slowest relay on your route. Tor is not a good choice for watching high-quality streaming videos or doing anything else that requires a high speed connection.
- Anyone can set up an exit node to spy on users. Since the traffic at the exit node is unencrypted, anyone (government, hacker, etc.) that is running the exit node can see your internet traffic if you are not using an HTTPS connection.
- You can only access the Tor network using their browser or from applications that have Tor access built in. If you need to use another browser because of that browser’s unique capabilities, you will not be protected by Tor.
- Tor nodes are free to use and run by volunteers, so there is no accountability or direct funding to maintain them.
- Since Tor is used by people who want to hide extremely sensitive information, frequent use can mark you for surveillance.
- Even those who do not want to hide extremely sensitive information can be at risk. For example, torrenting over Tor can allow peers to reveal your real IP address.
- Opening documents that were downloaded through Tor while your online also puts you at risk of revealing your IP address.
- You can get into a lot of trouble on the Dark Web (.onion sites), which can only be accessed with the Tor browser.

A VPN is a service that allows users to “borrow” the IP address of the VPN server and encrypts the connection between the user’s computer and the VPN server. It essentially acts on behalf of your computer, when you are online.
But it is much more secure than a proxy server because it encrypts your data, and some VPNs, like Hotspot Shield, do not log browsing history.
Since you can use the IP address of a VPN server in another part of the world, you can get around geographic content restrictions and mask your physical location. Read our complete guide on VPNs here.
VPN advantages
- A VPN is generally much faster than Tor. Since you are going directly to one VPN server, then to your desired destination (website, online service, etc.), it’s faster than through several Tor nodes, before going to your final destination.
- Free VPNs are available and are usually supported by advertisements.
- Funding from paid memberships pays for maintenance of the network and ensures the highest possible availability.
- A VPN protects all internet connections on your computer, not just the ones that are setup to work with Tor.
- Using a VPN that has a Kill Switch protects you from accidental data leaks.
- Allows you to access geographically restricted websites and content.
VPN disadvantages
- Some VPN providers can log your browsing history. Hotspot Shield does not.
- If you want to get rid of ads and access additional features, there is a small monthly cost.

The winner of Tor vs VPN
The bottom line is that the best solution for you will depend on your situation. Tor is best for people who are transmitting ultra sensitive information, which could literally result in life threatening situations. They are willing to sacrifice speed for security and they have set up the right processes and infrastructure to protect themselves from exit node surveillance.
A VPN is the best solution for a majority of people because it provides a great balance between browsing speed, ease of use, and privacy. It will also protect all online connections on your computer and no extra setup is needed.

What about using Tor with a VPN?
This is the most common question that comes up whenever we talk about Tor vs VPN. Although a VPN is generally faster than Tor, using them together will slow down your internet connection and should be avoided. More is not necessarily better in this situation.
Again, the best solution for most people is a VPN.
Still not sure which option is best for you? Download Hotspot Shield right now and try it for free.